/ Was ist ein Cloud Access Security Broker (CASB)?
Was ist ein Cloud Access Security Broker (CASB)?
Ein Cloud Access Security Broker (CASB) ist ein Durchsetzungspunkt zwischen Usern einer Cloud-Anwendung und Cloud-Diensten mit der Aufgabe, Data Protection- und Bedrohungsschutzdienste bereitzustellen. CASBs verhindern automatisch den Verlust sensibler Daten, stoppen Malware und andere Bedrohungen, erkennen und kontrollieren Schatten-IT, blockieren riskantes Teilen, setzen Sicherheitsrichtlinien wie Authentifizierung und Warnungen durch und stellen Compliance sicher.

Aktuelle Anwendungsszenarien
Mit zunehmender Cloud-Nutzung sind CASBs aufgrund ihrer verschiedenen Funktionen zur Gewährleistung von Cybersicherheit, Zugriffskontrolle und Data Protection zu einem Schlüsselelement der Unternehmenssicherheit geworden. Sie geben Ihnen die Kontrolle über Unternehmensdaten zurück, ob in Übertragung oder im Ruhezustand, in Cloud-Plattformen und Apps. CASBs sind aus folgenden Gründen von entscheidender Bedeutung:
- Die zunehmende Verbreitung und Nutzung von Cloud-basierten Plattformen und Anwendungen (Microsoft 365, Salesforce etc.) hat herkömmliche Netzwerksicherheits-Tools wie die im Rechenzentrum installierte Firewall weitgehend ihrer Wirksamkeit beraubt.
- IT-Teams verlieren zunehmend den Überblick – und damit die Kontrolle. Angesichts des breiten Spektrums Cloud-basierter Anwendungen, auf die User im Zuge ihrer Arbeit zugreifen, würde eine manuelle Verwaltung granularer Zugriffskontrollen die Kapazitäten so gut wie jede Organisation überfordern.
- Neben der Kontrolle der Shadow-IT können im Rahmen eines CASBs auch Richtlinien für Data Loss Prevention (DLP), SaaS Security Posture Management (SSPM) und Advanced Threat Protection bereitgestellt und durchgesetzt werden.
Die Rolle von CASBs für Unternehmen
Als Wächter der Aktivitäten in und um Cloud-Umgebungen – sie bieten Einblick in Aktivitäten, die Durchsetzung von Sicherheitsrichtlinien, die Erkennung von Bedrohungen und den Datenschutz – ermöglichen CASBs Unternehmen, die Cloud sicher zu nutzen und gleichzeitig die Kontrolle zu behalten und die Einhaltung gesetzlicher Vorschriften sicherzustellen. Schauen wir uns einige der konkreten Vorteile eines CASB genauer an.
Vorteile eines CASB
Eine effektive CASB-Lösung bietet im Rahmen einer ganzheitlichen Cloud-Sicherheitsstrategie entscheidende Vorteile:
Einblick in Schatten-IT und Risiken
Angesichts der Zunahme von Remote-Arbeit und BYOD benötigen Unternehmen klare Einblicke in die User, Geräte und SaaS-Anwendungen, die auf ihre Cloud-Umgebungen zugreifen. Damit steigt das Risiko eines unbefugten Zugriffs sprunghaft an. Ein CASB ermittelt die Cloud-App-Nutzung Ihres Unternehmens, erstellt Berichte zu Cloud-Ausgaben und bewertet das Risiko, um Sie bei der Erstellung und Aufrechterhaltung geeigneter Zugriffsrichtlinien zu unterstützen.
Cloud-Nutzungsmanagement
Die Nutzung der Cloud kann einer Reihe von Compliance-Anforderungen unterliegen, insbesondere in stark regulierten Branchen wie Finanzdienstleistungen, Gesundheitswesen und dem öffentlichen Sektor. Ein CASB kann branchenspezifische Risikofaktoren erkennen und bewerten sowie konsistente Datenschutzrichtlinien einrichten, um Sie bei der unternehmensweiten Einhaltung sämtlicher Compliance-Anforderungen zu unterstützen.
Datensicherheit und DLP
Das weltweite Datenvolumen verdoppelt sich alle zwei Jahre und das Datenrisiko nimmt entsprechend zu. Durch die Kombination eines CASB mit Cloud-DLP können Sie potenzielle Risiken erkennen und beheben. Durch Einblicke in sensible Inhalte, die zu, von oder zwischen Cloud-Umgebungen übertragen werden, haben Sie die besten Chancen, Vorfälle zu erkennen, Richtlinien durchzusetzen und die Sicherheit der Daten zu gewährleisten.
Bedrohungsabwehr
Im heutigen IT-Ökosystem sind Cloud-Ressourcen normalerweise am anfälligsten. Die Verhaltensanalysen und Bedrohungsinformationen eines effektiven CASB unterstützen eine zügige Erkennung und Blockierung verdächtiger Aktivitäten, gewährleisten zuverlässigen Schutz für cloudbasierte Anwendungen und Daten und stärken den Cloud-Sicherheitsstatus der Organisation.
So implementieren Sie einen CASB
Auf höchster Ebene geht es bei der Implementierung eines CASB darum, Ihre Bedürfnisse zu bewerten, sie dem richtigen Produkt zuzuordnen, es so einzurichten, dass es am besten zu Ihren Systemen passt, und fortlaufende Überwachungen und Audits durchzuführen. Die Implementierung kann in fünf Schritte eingeteilt werden:
- Bewerten Sie Ihre Umgebung und erstellen Sie einen Plan. Verstehen Sie die verwendeten Cloud-Dienste und Apps, die damit verbundenen Risiken sowie Ihre Sicherheitsrichtlinien und Compliance-Anforderungen.
- Wählen Sie die richtige CASB-Lösung für Ihre Anforderungen. Ebenso wichtig wie die Suche nach dem richtigen Produkt ist die Suche nach dem richtigen Anbieter – wählen Sie einen Partner, von dem Sie wissen, dass Sie ihm vertrauen können.
- Integrieren Sie den CASB in Ihre Cloud-Dienste und Anwenderverzeichnisse. Verwenden Sie SSO, um einen sicheren User-Zugriff und eine nahtlose Authentifizierung zu ermöglichen.
- Konfigurieren Sie Zugriffs-, Datenfreigabe-, DLP- und Sicherheitsrichtlinien. Abhängig von Ihrer Branche müssen Sie bei Ihren Richtlinien zur Verschlüsselung möglicherweise besondere Sorgfalt walten lassen.
- Ermöglichen Sie Echtzeitüberwachung und Bedrohungserkennung. Sie müssen Ihre Richtlinien außerdem regelmäßig überprüfen und aktualisieren, wenn sich die Anforderungen Ihres Unternehmens ändern.
Funktionsweise
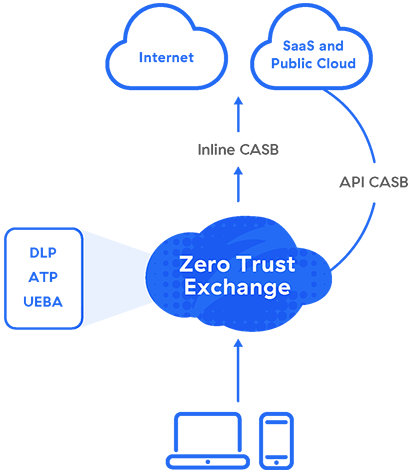
CASB-Lösungen können in Form von Hardware oder Software lokal implementiert werden. Am besten geeignet ist jedoch die Bereitstellung als Cloud-Service, die eine bessere Skalierbarkeit, niedrigere Kosten und unkomplizierte Verwaltung gewährleistet. Unabhängig vom Formfaktor können CASBs so eingerichtet werden, dass sie Proxying (Forward-Proxy oder Reverse-Proxy), APIs oder beides verwenden – als Multimode-CASB.
Proxy
CASBs müssen im Datenpfad ausgeführt werden und sollten daher am besten auf einer Cloud-Proxy-Architektur aufbauen. In der Mehrzahl der Fälle kommen dabei Weiterleitungsproxys zum Einsatz, die Datenschutz und Sicherheit clientseitig gewährleisten.
Ein Weiterleitungsproxy fängt Anforderungen für Cloud-Services auf dem Weg zu ihrem Ziel ab. Basierend auf den von Ihnen festgelegten Richtlinien setzt der CASB dann verschiedene sicherheitsrelevante Funktionen durch. Dazu zählt insbesondere die Überprüfung/Zuordnung von Zugangsdaten und Single Sign-On (SSO), Erstellung von Sicherheitsprofilen für einzelne Geräte, Protokollierung, Warnmeldungen, Malware-Erkennung, Verschlüsselung und Tokenisierung.
API
Ein Inline-Proxy fängt Daten bei der Übertragung ab. Zum Schutz ruhender Daten in der Cloud ist eine Out-of-band-Lösung erforderlich, die CASB-Anbieter durch Integrationen mit den Programmierschnittstellen (APIs) von Cloud-Service-Providern bereitstellen.
Was ist unter einem multimodalen CASB zu verstehen?
CASBs können im Proxy-Modus zur Inline-Durchsetzung von Richtlinien bereitgestellt werden. Dadurch lassen sich Datenverluste und Malware-Infektionen in Echtzeit verhindern. Sie können auch mit APIs integriert werden, um die Inhalte von SaaS-Anwendungen zu scannen, damit vertrauliche Daten sowie Ransomware und andere Bedrohungen erkannt und entsprechende Maßnahmen zu ihrem Schutz bzw. ihrer Abwehr durchgesetzt werden können. Inzwischen kommen verstärkt API-Integrationen im Rahmen von SaaS Security Posture Management (SSPM) zum Einsatz, um Fehlkonfigurationen in Anwendungen zu beheben.
CASBs, die wahlweise im Proxy- oder API-Modus bereitgestellt werden können, werden als multimodale CASBs bezeichnet. Über die Absicherung von SaaS hinaus lassen sich damit auch IaaS-Lösungen wie Microsoft Azure und AWS S3 schützen. Im Idealfall sollte der CASB nicht als zusätzliches Einzelprodukt, sondern im Rahmen einer SSE-Plattform implementiert werden. Dadurch wird ein einheitliches Sicherheitsniveau, verbesserte Performance und vereinfachte Verwaltung durch Konsolidierung gewährleistet.
Gartner: Von CASB zu SASE
Gartner definierte „CASB“ erstmals im Jahr 2012, als Unternehmen die Technologie hauptsächlich zur Kontrolle der Schatten-IT nutzten.
Die Vorteile und Fähigkeiten von CASB begannen sich immer mehr mit Secure Web Gateways (SWG) zu überschneiden, und im Jahr 2019 definierte Gartner die Secure Access Service Edge (SASE), ein Framework aus cloudbasierten Diensten, die „umfassende WAN-Funktionen mit umfassenden Netzwerksicherheitsfunktionen“ bieten (wie SWG, CASB, FWaaSund ZTNA), um die dynamischen sicheren Zugriffsanforderungen digitaler Unternehmen zu unterstützen.“
Im Zuge der weiteren Ausdifferenzierung des Konzepts schuf Gartner 2021 den Begriff Security Service Edge (SSE) als Bezeichnung für die sicherheitsorientierte Komponente von SASE. Berücksichtigt wird damit auch das branchenübergreifende Bemühen um Straffung komplexer und disparater Security-Stacks. Laut Prognosen von Gartner ist davon auszugehen, dass 30 % der Unternehmen bis 2024 auf ganzheitliche Lösungen umsteigen, die SWG-, CASB-, ZTNA- und FWaaS-Funktionen (Firewall-as-a-Service) aus einer Hand bereitstellen.
CASB und SASE
CASB und SASE ergänzen einander, wobei CASB Cloud-Interaktionen und Datenflüsse sichert, während SASE Cloud-Sicherheit, Netzwerk und Zugriffskontrolle umfassender integriert. SASE beinhaltet per Definition CASB und ermöglicht es Unternehmen, Richtlinien durchzusetzen und Daten als Teil ihrer Netzwerkarchitektur zu sichern.
Die wichtigsten Anwendungsfälle für CASB
1. Erkennen und Kontrollieren von Shadow-IT
Wenn unternehmenseigene Dateien und Daten in Cloud-Anwendungen gespeichert und zur gemeinsamen Nutzung freigegeben werden, die nicht offiziell von der IT genehmigt sind, ist ihre Sicherheit gegebenenfalls nicht gewährleistet. Zur Bewältigung dieses Risikos müssen Organisationen einen transparenten Überblick über sämtliche Cloud-Anwendungen behalten, mit denen ihre User arbeiten, und diese entsprechend absichern.
Zscaler CASB erkennt automatisch sogenannte Shadow-IT und deckt riskante Anwendungen auf, auf die User zugreifen. Automatische, einfach konfigurierbare Richtlinien erzwingen dann die jeweils angemessenen Maßnahmen für einzelne Anwendungen bzw. für Anwendungskategorien: zulassen oder blockieren, Hochladen verhindern, Nutzung einschränken usw.
2. Absicherung privater SaaS-Instanzen
Womöglich verwenden Mitarbeiter sowohl eine von der IT-Abteilung genehmigte und eine inoffizielle Instanz von Anwendungen wie Google Drive. Je nachdem, ob die betreffende Anwendung komplett zugelassen oder komplett blockiert wird, ist die Konsequenz entweder die unzulässige Frei- bzw. Weitergabe von Daten oder aber eine Beeinträchtigung der Produktivität.
Zscaler CASB unterscheidet zwischen genehmigten SaaS-Mandanten und nicht genehmigten Instanzen und setzt die jeweils angemessenen Richtlinien durch. Vorkonfigurierte Kontrollfunktionen für SaaS-Mandanten ermöglichen eine automatische Korrektur in Echtzeit.
3. Kontrollieren riskanter Dateifreigaben
Cloud-basierte Anwendungen ermöglichen Zusammenarbeit und gemeinsame Nutzung von IT-Ressourcen in bisher ungekanntem Ausmaß. Damit vertrauliche Unternehmensdaten nicht in falsche Hände geraten, müssen die Sicherheitsbeauftragten die Kontrolle darüber behalten, wer in genehmigten Anwendungen welche Daten und Dateien zur gemeinsamen Nutzung freigeben bzw. darauf zugreifen darf.
Verwaltungsfunktionen für Kooperationssoftware sind ein unverzichtbarer Bestandteil jedes effektiven CASB. Zscaler CASB unterstützt ein zügiges und wiederholtes Crawlen von Dateien in SaaS-Instanzen. Dabei werden vertrauliche Daten erkannt und die User überprüft, an die sie weitergeleitet bzw. freigegeben werden. Auf verdächtige Filesharing-Praktiken wird entsprechend reagiert.
4. Korrektur von SaaS-Fehlkonfigurationen
Bei der Bereitstellung und Verwaltung von Cloud-basierten Anwendungen ist unbedingt auf präzise Konfiguration zu achten, damit alle Anwendungen reibungslos funktionieren und sicher damit gearbeitet werden kann. Fehlkonfigurationen beeinträchtigen die Sicherheit und erhöhen das Risiko von Datenexpositionen.
Zscaler SSPM lässt sich über eine API mit SaaS-Instanzen integrieren, um nach Fehlkonfigurationen zu suchen, die die Compliance mit den geltenden Vorschriften gefährden könnten. Neben SSPM sind CSPM und CIEM als weitere Komponenten in Zscaler Workload Posture inbegriffen.
5. Verhindern von Datenverlusten
Mindestens ebenso wichtig wie die Erkennung von Fehlkonfigurationen, die Datenpannen und -verluste begünstigen können, ist die Fähigkeit, die Speicherorte vertraulicher Daten in der Cloud zu erkennen und entsprechend zu schützen. Ein Großteil dieser Daten unterliegt Frameworks wie unter anderem der HIPAA, PCI DSS oder der DSGVO.
Die Zero Trust Exchange, unsere cloudnative Sicherheitsplattform, bietet einheitlichen Datenschutz mit Cloud- DLP- und CASB-Funktionen. So wird sichergestellt, dass Cloud-Anwendungen richtig konfiguriert sind, um Datenverlust und Verstöße gegen Vorschriften zu verhindern. Durch hochentwickelte Techniken zur Klassifizierung können vertrauliche Daten an sämtlichen Speicherorten und auf allen Übertragungswegen erkannt und gesichert werden.
6. Verhindern von Angriffen
Eine einzige schädliche Datei, die in eine der genehmigten Cloud-Anwendungen gelangt, kann innerhalb kürzester Zeit auf andere Anwendungen übergreifen bzw. die Geräte anderer User infizieren. Deswegen brauchen Organisationen eine effektive Methode, um sich in Echtzeit gegen Bedrohungen beim Hochladen und im Ruhezustand zu schützen.
Zscaler CASB setzt eine Kombination von ATP-Funktionen (Advanced Threat Protection) zur Abwehr von Malware ein:
- Echtzeit-Proxy – verhindert das Hochladen schädlicher Dateien in die Cloud
- Out-of-Band-Scan – erkannt Daten im Ruhezustand und behebt Risiken
- Cloud-Sandboxing – erkennt Zero-Day-Malware
- Agentenlose Cloud Browser Isolation – gewährleistet sicheren Zugriff von nicht verwalteten Endgeräten
Zscaler CASB
In der ganzheitlichen Zscaler Zero Trust Exchange™ ist ein multimodaler CASB ebenso inbegriffen wie SWG, ZTNA und weitere Funktionen. Damit unterstützt Zscaler Organisationen im Bemühen um Konsolidierung von Einzelprodukten zur Reduzierung der IT-Komplexität, wobei der gesamte Traffic in einem einzigen Arbeitsgang überprüft wird. Für Administratoren beschränkt sich der Aufwand auf die Konfiguration einer automatisierten Richtlinie, die konsistente Sicherheit in allen Cloud-Datenkanälen gewährleistet.
Inline-Sicherheit für Daten bei der Übertragung
Durch den leistungsstarken Weiterleitungsproxy mit SSL-Überprüfung wird zuverlässiger Echtzeitschutz für unternehmenskritische Ressourcen gewährleistet:
- Durch Erkennung von Shadow-IT und Kontrolle Cloud-basierter Anwendungen können inoffiziell genutzte Anwendungen erkannt und geschützt werden – ganz ohne Netzwerkgeräteprotokolle.
- DLP-Maßnahmen verhindern das Hochladen vertraulicher Daten in genehmigte sowie inoffiziell genutzte Anwendungen.
- Advanced Threat Protection blockiert bekannte und unbekannte Malware in Echtzeit mit ML-gestützter Cloud Sandbox
- Cloud Browser Isolation gewährleistet, dass Sitzungen auf nicht verwalteten Geräten (BYOD) als Pixel gestreamt werden, um Datenlecks ohne Einsatz von Reverseproxys zu verhindern.
Out-of-band-Sicherheit für Daten im Ruhezustand
Durch API-basiertes Scannen von SaaS-Anwendungen, Cloud-Plattformen und deren Inhalten wird die Unternehmenssicherheit automatisch verbessert:
- Mit vordefinierten sowie kundenspezifisch anpassbaren DLP-Wörterbüchern lassen sich vertrauliche Daten in SaaS-Umgebungen und öffentlichen Clouds identifizieren.
- Mithilfe von Funktionen zum Management der Zusammenarbeit werden Anwendungen auf riskante Dateifreigaben geprüft und diese gemäß den Richtlinien verhindert.
- Cloud-Sandbox-Technologie scannt ruhende Daten zur Erkennung und Abwehr von Zero-Day-Malware und -Ransomware
- SSPM, CSPM und CIEM überprüfen SaaS- und IaaS-Konfigurationen sowie -Berechtigungen, um Probleme automatisch zu beheben.
Empfohlene Ressourcen
Häufig gestellte Fragen
Jede Organisation mit wichtigen Daten und Apps, die in Cloud-Diensten gespeichert sind, sollte einen CASB verwenden. Er überwacht und steuert die zwischen Ihrem Netzwerk und der Cloud gesendeten Daten, um Compliance sicherzustellen, Leaks zu verhindern und unbefugten Zugriff zu stoppen. CASBs tragen dazu bei, die Transparenz und Kontrolle über sensible Daten aufrechtzuerhalten und viele inhärente Sicherheitsrisiken der Cloud zu bewältigen.
Ein CASB fungiert als Kontrollpunkt zwischen Ihrem Netzwerk und Cloud-Diensten, überwacht und verwaltet den Datenverkehr zu und von Cloud-Apps, bietet Einblick in User-Aktivitäten, setzt Sicherheitsrichtlinien durch, erkennt Bedrohungen und schützt sensible Daten. CASBs tragen dazu bei, die Kontrolle, Compliance und den Datenschutz für Ihre Netzwerk-Cloud-Umgebung aufrechtzuerhalten.
Um das richtige CASB für Ihr Unternehmen zu finden, bewerten Sie zunächst, was Sie schützen müssen und in welchem Umfang und welche Cloud-Dienste Sie nutzen. Der richtige CASB bietet eine robuste Bedrohungserkennung, granulare Zugriffskontrollen, starke Verschlüsselung und Integration in Ihre bestehende Sicherheitsinfrastruktur und Cloud-Umgebung. Schließlich möchten Sie den richtigen Technologiepartner finden – einem, dem Sie vertrauen können, wenn er mit Ihnen zusammenarbeitet, um die von Ihnen gewählte CASB-Lösung so zu gestalten, dass sie Ihren Anforderungen am besten entspricht.
Viele CASBs verfügen über DLP-Funktionen, um zu verhindern, dass sensible Daten ohne Autorisierung von Ihrem Netzwerk in die Cloud gelangen (oder umgekehrt). DLP-Funktionen überwachen den Datenverkehr, blockieren oder verschlüsseln sensible Daten und senden Warnungen bei potenziellen Verstößen oder Lecks. Gemeinsam tragen CASB und DLP dazu bei, die Bewegung von Daten zu kontrollieren und sensible Informationen zu schützen, die zwischen lokalen Netzwerken und Cloud-Diensten übertragen werden.
Ein CASB ist ein wesentlicher Bestandteil einer starkenCloud-Sicherheit, aber nicht der einzige. Effektive Cloud-Sicherheit kombiniert CASB mit robustem Identitäts- und Zugriffsmanagement, Verschlüsselung, Netzwerksicherheit, regelmäßigen Sicherheitsüberprüfungen und mehr. CASB konzentriert sich auf die Sicherung des Datenflusses zwischen dem Netzwerk eines Unternehmens und der Cloud, umfassende Cloud-Sicherheit deckt jedoch ein breiteres Spektrum potenzieller Bedrohungen in allen Aspekten der Cloud-Infrastruktur und -Nutzung ab.



