Zscaler Blog
Erhalten Sie die neuesten Zscaler Blog-Updates in Ihrem Posteingang
Abonnieren
So gelingt der erfolgreiche Umstieg auf M365: Remote-Arbeit als Vorlage für die Transformation
Dieser Artikel erschien auch auf LinkedIn.
Nachdem die unmittelbaren Auswirkungen der COVID-Pandemie ausgestanden sind, erscheint es angebracht, die Entscheidungen und Maßnahmen, die im IT-Bereich zu ihrer Bewältigung getroffen wurden, Revue passieren zu lassen: Was haben wir damals richtig gemacht, welche Maßnahmen erwiesen sich rückblickend als weniger zielführend, und was können wir daraus für die Zukunft lernen?
In meinem früheren Job in der Planung und Implementierung von Netzwerk- und Sicherheitsarchitekturen würde ich den jetzigen Zeitpunkt als Chance nutzen, das Wertschöpfungspotenzial der damals eingeführten Veränderungen in vollem Umfang zu realisieren – Veränderungen, die eine erfolgreiche und produktive Umstellung auf dezentrale Arbeitskonzepte in den Fachabteilungen ermöglichten. Unter anderem setzte sich dabei die Erkenntnis durch, dass herkömmliche perimeterbasierte Netzwerksicherheitslösungen sich aufgrund ihrer mangelnden Skalierbarkeit nur sehr bedingt zur Unterstützung von Remote-Arbeit eignen. Das gilt insbesondere für Anwendungen mit hohen Traffic-Volumen wie Microsoft 365 (M365). Einmal abgesehen von den erhöhten Kosten, die durch Backhauling Traffics entstehen, führt das Tunneling des gesamten M365-Traffics zu deutlichen Performance-Einbußen und kann im schlimmsten Fall zum Fehlschlagen des M365-Deployments führen.
Altlasten aus der Vergangenheit
Die Modernisierung der IT-Architektur hat für CIOs hohe Priorität. Eine zentrale Rolle spielt dabei oft die Implementierung von M365 zur Optimierung der Produktivität in geografisch stark distribuierten Umgebungen. Die unternehmensweite Umstellung auf M365 setzt indes eine umfassende Überprüfung der Methoden zur Verarbeitung und Sicherung des Traffics voraus. Microsoft empfiehlt, den Traffic von M365-Anwendungen möglichst zügig über lokale Breakouts zu routen und dabei keine zusätzlichen Sicherheitskontrollen anzuwenden, da er sowieso aus einer sicheren Quelle stamme. Für die Mehrzahl der Organisationen ist dies jedoch keine realistische Option – und zwar aus mehreren Gründen nicht:
- Der gesamte Zweigstellen-Traffic (einschließlich des Traffics von Remote-Mitarbeitern) wird über eine Hub-and-Spoke-Architektur verarbeitet.
- Es besteht keine Möglichkeit zur Einrichtung von Split-Tunnel-Architekturen oder lokalen Breakouts (z. B. über SD-WAN).
- Die Organisation wendet unantastbare Legacy-Sicherheitsrichtlinien an.
Bei herkömmlichen Hub-and-Spoke-Modellen wird der gesamte Internet-Traffic vom User über das Unternehmensnetzwerk zum Internet geroutet. Durch die Implementierung von M365 vervielfacht sich das Traffic-Volumen – das führt zur Überlastung des Unternehmensnetzwerks.
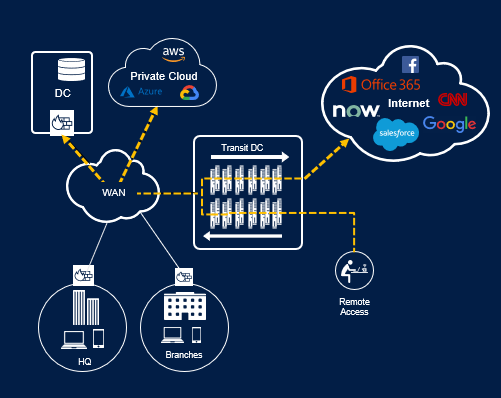
Abb. 1. Verarbeitung des Traffics zum Internet mit einer perimeterbasierten Sicherheitslösung
Zusätzlich zum regulären M365-Traffic fallen regelmäßig Anwendungsupdates für Hunderte oder gar Tausende von Usern an, die die Infrastruktur-Kapazitäten des Unternehmens schnell überfordern. Wenn die Implementierung einer „Productivity Software“ wie M365 dazu führt, dass IT-Teams Probleme haben, die Produktivität der Mitarbeiter zu gewährleistet, sind Frustrationen vorprogrammiert – und Zweifel am Sinn der Umstellung auf M365 durchaus nachvollziehbar.
Die bloße Hochskalierung der vorhandenen physischen Netzwerkkapazitäten ist ebenfalls keine gute Lösung. Mit der physischen Netzwerkkapazität verdoppeln sich häufig auch die Betriebskosten für Ihr WAN (ganz zu schweigen von den Investitionskosten für neue Geräte). Das Problem wird dadurch nicht dauerhaft gelöst, sondern gemäß dem Mooreschen Gesetz bestenfalls um ein Jahr aufgeschoben. Außerdem gewinnen Sie weder Wohlwollen noch Vertrauen bei der Geschäftsführung. Die M365-Implementierung ist damit womöglich von vornherein zum Scheitern verurteilt.
Eine effektivere Alternative für die Zukunft
Ich habe einen besseren Vorschlag: Machen Sie das Internet zu Ihrem neuen Unternehmensnetzwerk. Der Nachweis, dass das Internet eine sichere Alternative zum Unternehmensnetzwerk als Transportlösung darstellt, zählt zu den wenigen positiven Ergebnissen der Pandemie.
COVID-19 zwang Unternehmen zur schlagartigen Umstellung ihrer gesamten Belegschaft auf Remote-Arbeit. Jeder Mitarbeiter im Homeoffice fungierte quasi als Zweigstelle mit einem einzigen User. Die Überflutung der Legacy-Unternehmensnetzwerke durch den Traffic, den diese Mini-Zweigstellen generierten (und der in vielen Fällen über VPNs geleitet wurde), beeinträchtigte die Performance auf Anwendungs- und Netzwerkebene. Als sinnvollere Alternative bietet sich an, Usern den Zugriff auf cloudbasierte Anwendungen direkt über ihre lokalen Internetverbindungen zu ermöglichen. Diese Direktverbindungen müssen jedoch unbedingt abgesichert werden.
Zur Lösung dieses Problems kombinierten viele Unternehmen den Direktzugang zum Internet mit Inline-Cloud-Sicherheitslösungen. Dadurch entfällt die Notwendigkeit, den gesamten Traffic – unabhängig vom Standort des Users bzw. der jeweiligen Hosting-Umgebung der Anwendung – im Backhauling-Verfahren über komplexe perimeterbasierte Security-Stacks umzuleiten. Stattdessen werden User übers Internet direkt mit der gewünschten Anwendung verbunden. Durch direkte und sichere Weiterleitung des Traffics zum jeweiligen Verbindungsziel ohne Backhauling werden Latenzen reduziert. Außerdem ersparen Unternehmen sich den Aufwand, der mit der Einrichtung und Verwaltung komplexer perimeterbasierter Security-Stacks an ihren Standorten bzw. Zweigstellen verbunden ist.
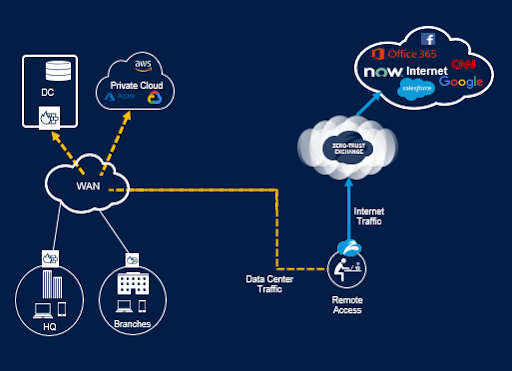
Abb. 2. Direktverbindungen zum Internet für Internet- und SaaS-Workloads
Der Einsatz einer Inline-Sicherheitslösung hat gleich mehrere Vorteile:
- Entlastung des Netzwerks durch lokale Internet-Breakouts (der Traffic zum Internet macht bis zu 60 % des Gesamtvolumens aus)
- Geringere Latenzen, da der Traffic zu cloudbasierten Anwendungen direkt in die Cloud geroutet wird
- Kostensenkung durch Rückgang des MPLS-Traffics
- Remote-User profitieren von unternehmensspezifischen Sicherheitslösungen auf Perimeterebene
- Optimierung der Sicherheit und Performance durch mehr Transparenz über User- und Workload-Aktivitäten
Die Notwendigkeit zur Umstellung auf Remote-Arbeit im Zuge der Pandemie gab einen hervorragenden Testfall für die beschleunigte M365-Implementierung ab. Dabei wurde erfolgreich der Nachweis erbracht, dass direkte Internetverbindungen standortunabhängig für alle User eine Anwendererfahrung ermöglichen, die dem „On-Permise“-Zugriff entspricht. Anhand dieses Testfalls können Sie überprüfen, inwieweit direkte Internetverbindungen für Ihre konkreten Anwendungsszenarien möglicherweise Vorteile gegenüber Legacy-Architekturen aufweisen.
Der Einsatz einer Inline-Cloud-Sicherheitslösung ermöglicht die Nutzung des Internets als wesentliches Element Ihrer Strategie zur Gewährleistung der Konnektivität. Dadurch werden die negativen Auswirkungen des wachsenden Traffics über WAN/MPLS-Verbindungen durch Remote-Mitarbeiter minimiert.
Im Vorfeld der Umstellung auf eine cloudbasierte Sicherheitslösung sollten Sie unbedingt in Zusammenarbeit mit den zuständigen Infrastruktur-Teams Ihre Sicherheitsstrategie einer gründlichen Analyse unterziehen. So können Sie feststellen, inwieweit aktuelle Richtlinien, Sachzwänge und Governance-Prozesse möglicherweise Ihren Handlungsspielraum zur Einrichtung von Direktverbindungen zu Cloud-Anwendungen durch zusätzliche lokale Internet-Breakouts einschränken.
Gartner verwendet den Begriff „Thin Branch/Heavy Cloud“ zur Bezeichnung von Architekturmodellen gemäß dem SASE-Framework (Secure Access Service Edge), die die Sicherheit aus dem physischen Netzwerk in die Cloud verlagern. Wir empfehlen Ihnen, sich an diesem Modell zu orientieren und Ihre Netzwerkarchitektur nicht mit unnötigen Produkten zu verkomplizieren, wenn Sie stattdessen den Traffic einfach direkt übers Internet leiten können.
Zero Trust reduziert die Abhängigkeit von Legacy-Architekturen
Eine Zero-Trust-basierte Cloud-Sicherheitslösung kann Sie dabei unterstützen, das Potenzial Ihrer Investitionen in Productivity Software sowie Ihrer COVID-bedingten Maßnahmen voll auszuschöpfen und die M365-Implementierung zu beschleunigen. Bei der Auswahl geeigneter Lösungen zur Vereinfachung der Netzwerk- und Sicherheitsarchitektur gemäß dem SASE-Framework ist eine enge Zusammenarbeit zwischen allen Verantwortlichen erforderlich, die für Netzwerkarchitektur, User Experience und Sicherheit zuständig sind.
Durch sichere Verlagerung des Traffics ins Internet entlasten Sie Ihr Netzwerk und reduzieren Ihre Abhängigkeit von Legacy-Netzwerk- und Sicherheitsarchitekturen. Dadurch beschleunigen Sie wiederum die M365-Implementierung, steigern die Produktivität und erzielen letztlich bessere Geschäftsergebnisse. Das plötzliche Anschwellen der Remote-Belegschaft bietet Ihnen eine einmalige Chance, anhand eines Testfalls nachzuweisen, dass eine erfolgreiche M365-Implementierung mit Direktverbindungen zum Internet in der Praxis möglich ist. Diese User liefern den unwiderlegbaren Beweis dafür, dass das Internet sicher als Transportschicht verwendet werden und dadurch die digitale Transformation beschleunigen kann.
War dieser Beitrag nützlich?
Haftungsausschluss: Dieser Blog-Beitrag wurde von Zscaler ausschließlich zu Informationszwecken erstellt und wird ohne jegliche Garantie für Richtigkeit, Vollständigkeit oder Zuverlässigkeit zur Verfügung gestellt. Zscaler übernimmt keine Verantwortung für etwaige Fehler oder Auslassungen oder für Handlungen, die auf der Grundlage der bereitgestellten Informationen vorgenommen werden. Alle in diesem Blog-Beitrag verlinkten Websites oder Ressourcen Dritter werden nur zu Ihrer Information zur Verfügung gestellt, und Zscaler ist nicht für deren Inhalte oder Datenschutzmaßnahmen verantwortlich. Alle Inhalte können ohne vorherige Ankündigung geändert werden. Mit dem Zugriff auf diesen Blog-Beitrag erklären Sie sich mit diesen Bedingungen einverstanden und nehmen zur Kenntnis, dass es in Ihrer Verantwortung liegt, die Informationen zu überprüfen und in einer Ihren Bedürfnissen angemessenen Weise zu nutzen.
Erhalten Sie die neuesten Zscaler Blog-Updates in Ihrem Posteingang
Mit dem Absenden des Formulars stimmen Sie unserer Datenschutzrichtlinie zu.




