The vast majority of public cloud security incidents are the customer’s own fault. Most prominent among these has been the huge number of AWS S3 bucket exposures over the last several years, with big names like Verizon, Accenture, the Republican National Committee, and even The Pentagon falling victim.
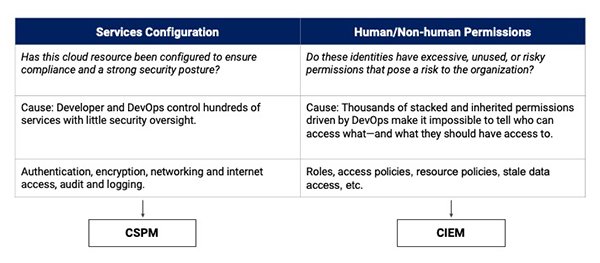
While these incidents might have gotten an inordinate amount of press coverage, they are far from the only type of issue causing security incidents in the public cloud. From a macro standpoint, these issues fall under two categories: misconfigurations and excessive permissions.
Two new categories of tools, Cloud Security Posture Management (CSPM) and Cloud Infrastructure Entitlement Management (CIEM), have emerged to solve these challenges. The question is, which technology will better help you reduce risk while embracing public cloud?
Reducing public cloud misconfigurations
CSPM tools are built to solve public cloud misconfiguration issues, such as the aforementioned AWS S3 bucket exposures. Across the big three cloud providers, Microsoft Azure offers more than 600 services, AWS over 200, and GCP over 100 distinct services. Each of these services has configuration options that impact security and risk, and they are evolving very rapidly. With most organizations now adopting a multicloud strategy, there are thousands of feature configurations for infosec teams to monitor.
CSPM tools help organizations monitor and prioritize configuration issues across their public cloud environments, addressing both security and compliance requirements. These tools inventory everything running across multi-cloud deployments, calculate security posture across 100s of services, use risk to prioritize issues, automatically remediate, and then enforce guardrails to ensure ongoing compliance.
Addressing excessive public cloud permissions
CIEM is a newer category than CSPM, built to address security gaps left by CSPM tools that focus exclusively on misconfigurations. These tools address the inadequate control over identities and privileges that has become prevalent in public cloud deployments. An organization with hundreds of cloud users and tens of thousands of resources will have tens of millions of individual entitlements to manage—this is far from a human-scale problem.
CIEM helps organizations discover who can access what, how permissions are utilized across human and non-human identities, build and enforce a simple and transparent least-privileged permissions model, and implement a multicloud guardrail policy for entitlements.
CSPM vs. CIEM: Which do you need?
So, given the importance of these tools for reducing cloud risk, which do you need to deploy in your environment?
The answer is both.
Misconfigurations and excessive permissions are both major causes of public cloud security incidents that need to be addressed. Together, these products can minimize the vast majority of issues that have plagued cloud security to date.
With our recent acquisition of Trustdome and their innovative CIEM platform, Zscaler has bundled CIEM and CSPM together as part of our comprehensive Zscaler Cloud Protection (ZCP) solution. I’d encourage you to reach out to Zscaler to take a closer look at how we can help address the biggest sources of risk in your public cloud deployments.






